
Protect Your Business from Every Angle
Your network is only as strong as its weakest link. We find the vulnerabilities before attackers do, and architect solutions that keep your data safe.
Trust & Compliance
Ohio State-Insured
All insurance required to bid and work within Ohio state agencies.
NIST CSF 2.0 + ORC 9.64
We align you to NIST Cybersecurity Framework 2.0 and report to the state on ORC 9.64 on your behalf.
SOX-Grade Experience
Multi-year programs delivered in publicly-traded, SOX-controlled environments. Case study.
Our Security Services
A comprehensive approach to securing your wired, wireless, cloud, and on-premises environments.
Wired Penetration Testing
We simulate real-world attacks against your internal network to identify exploitable vulnerabilities in switches, firewalls, servers, and endpoints.
Wireless Penetration Testing
Targeted testing of your WiFi infrastructure, including rogue access point detection, WPA/WPA2/WPA3 assessment, and guest network isolation verification.
WiFi Site Surveys
Predictive and active site surveys to optimize access point placement, eliminate dead zones, and ensure consistent coverage throughout your facility.
Network Architecture
Design and review of your network topology, VLAN segmentation, firewall rules, and access control lists to ensure defense-in-depth.
Network Troubleshooting
Diagnosing and resolving persistent network issues including latency, packet loss, intermittent connectivity, and performance bottlenecks.
Security Assessments
Comprehensive audits of your security posture covering policies, procedures, technical controls, and employee awareness readiness.
Our Assessment Process
A structured approach to identifying and remediating security risks.
Reconnaissance
We map your environment, identify attack surfaces, and define the scope and rules of engagement for testing.
Testing & Analysis
Active testing using industry-standard tools and methodologies, followed by detailed analysis of every finding.
Report & Remediate
A detailed report with risk-ranked findings, remediation steps, and a follow-up retest to confirm vulnerabilities are resolved.
Purpose-Built Security Tooling
We don't rely solely on off-the-shelf scanners. Our netvuln-tool platform was built in-house to deliver faster, more actionable vulnerability assessments.
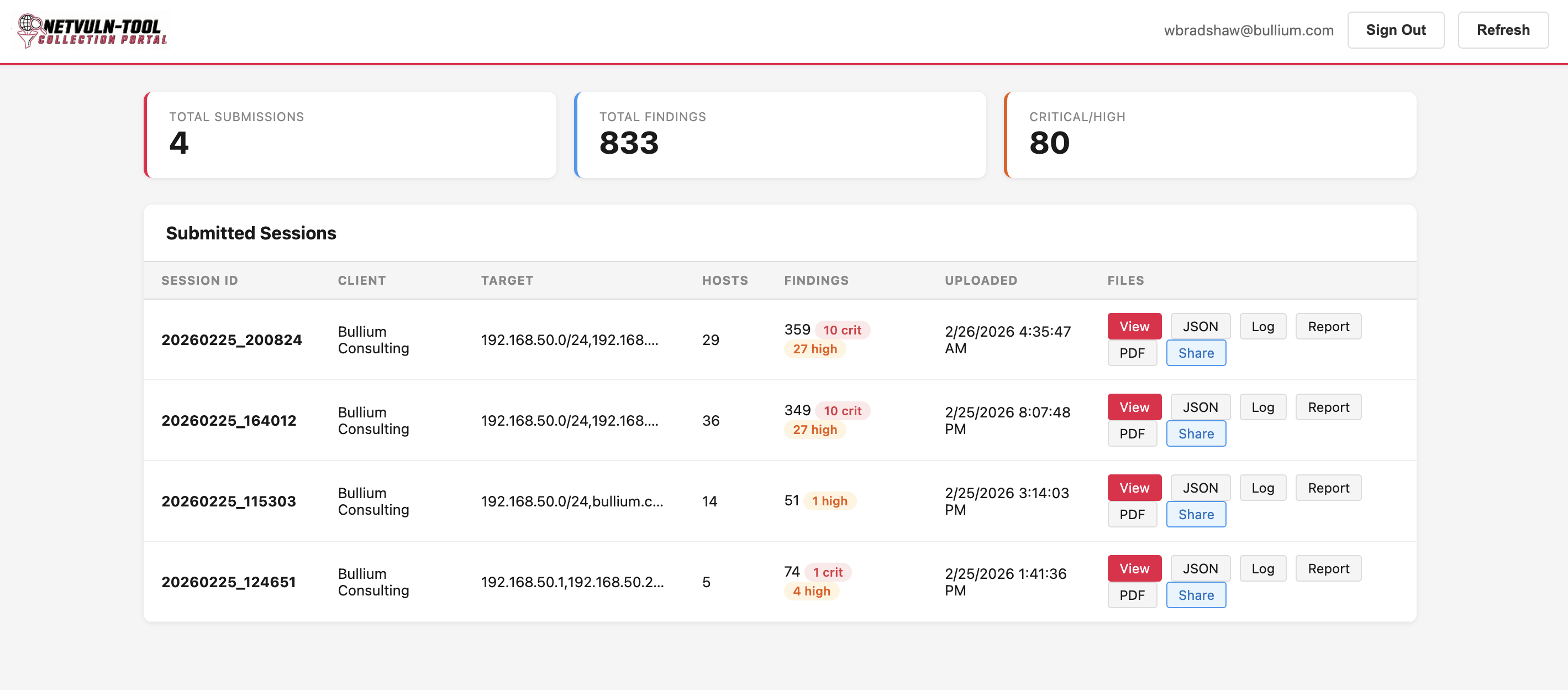

Centralized Vulnerability Management
Every assessment we run is tracked through our netvuln-tool collection portal. Clients get full visibility into total findings, severity breakdowns, and session history, all in one place.
The portal aggregates data across multiple scan sessions, giving you a clear picture of how your security posture evolves over time as vulnerabilities are discovered and remediated.
- Real-time severity breakdown (Critical, High, Medium, Low)
- Session-level detail with host counts and findings
- Export to JSON, PDF, and CSV for compliance documentation
- Secure token-based report sharing with stakeholders
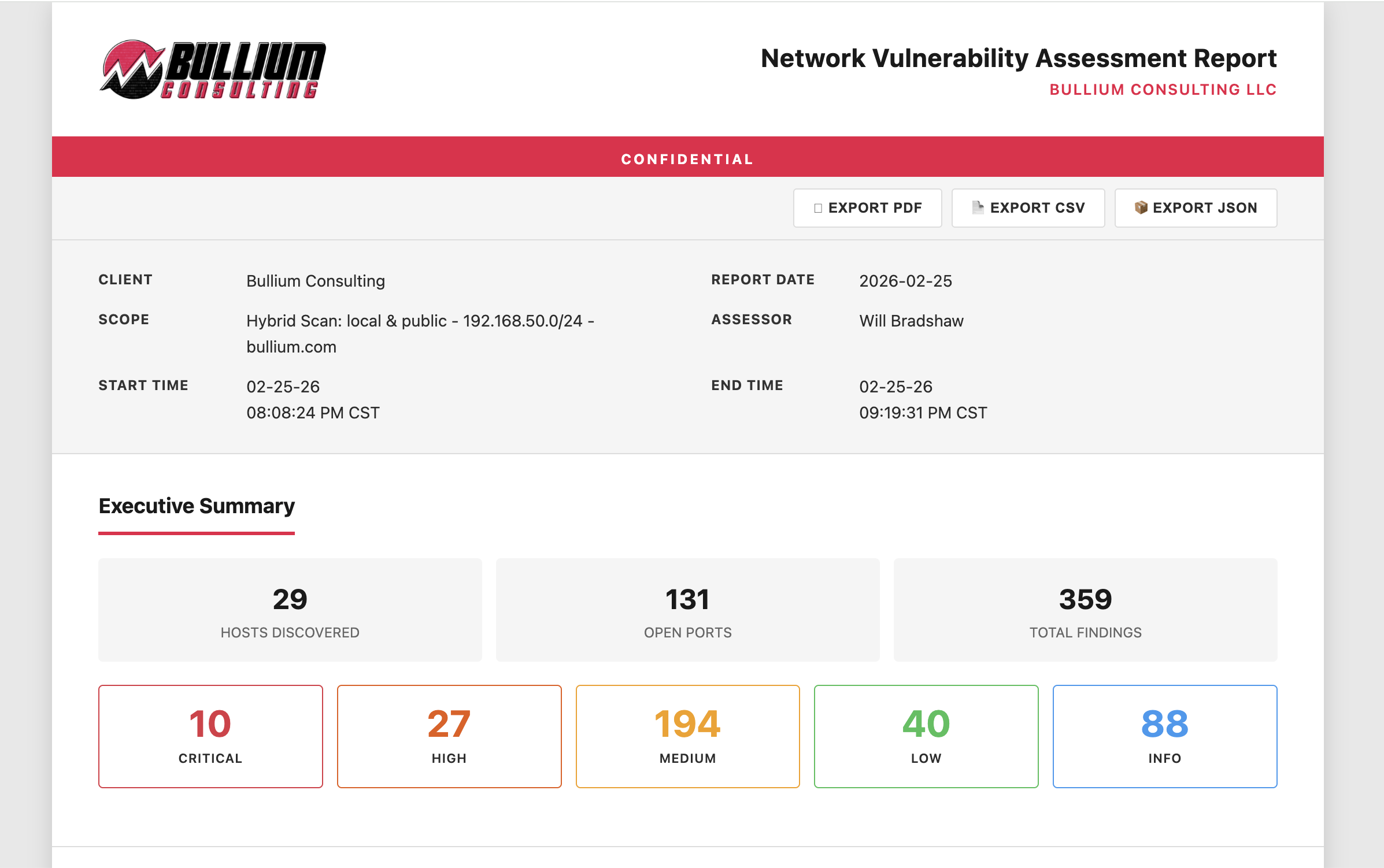
Branded Assessment Reports You Can Share
Every engagement produces a professionally branded Network Vulnerability Assessment Report. The executive summary gives leadership an immediate understanding of scope and risk, while detailed findings give your technical team exactly what they need to remediate.
Reports include host discovery counts, open port enumeration, and every finding categorized by severity, from critical vulnerabilities requiring immediate attention to informational items for your records.
- Executive summary with hosts discovered, open ports, total findings
- Color-coded severity breakdown (Critical through Info)
- One-click export to PDF, CSV, or JSON
- Shareable via secure, token-protected link
See how our assessment process and tooling can uncover risks in your environment.
Schedule Your Network Security Assessment
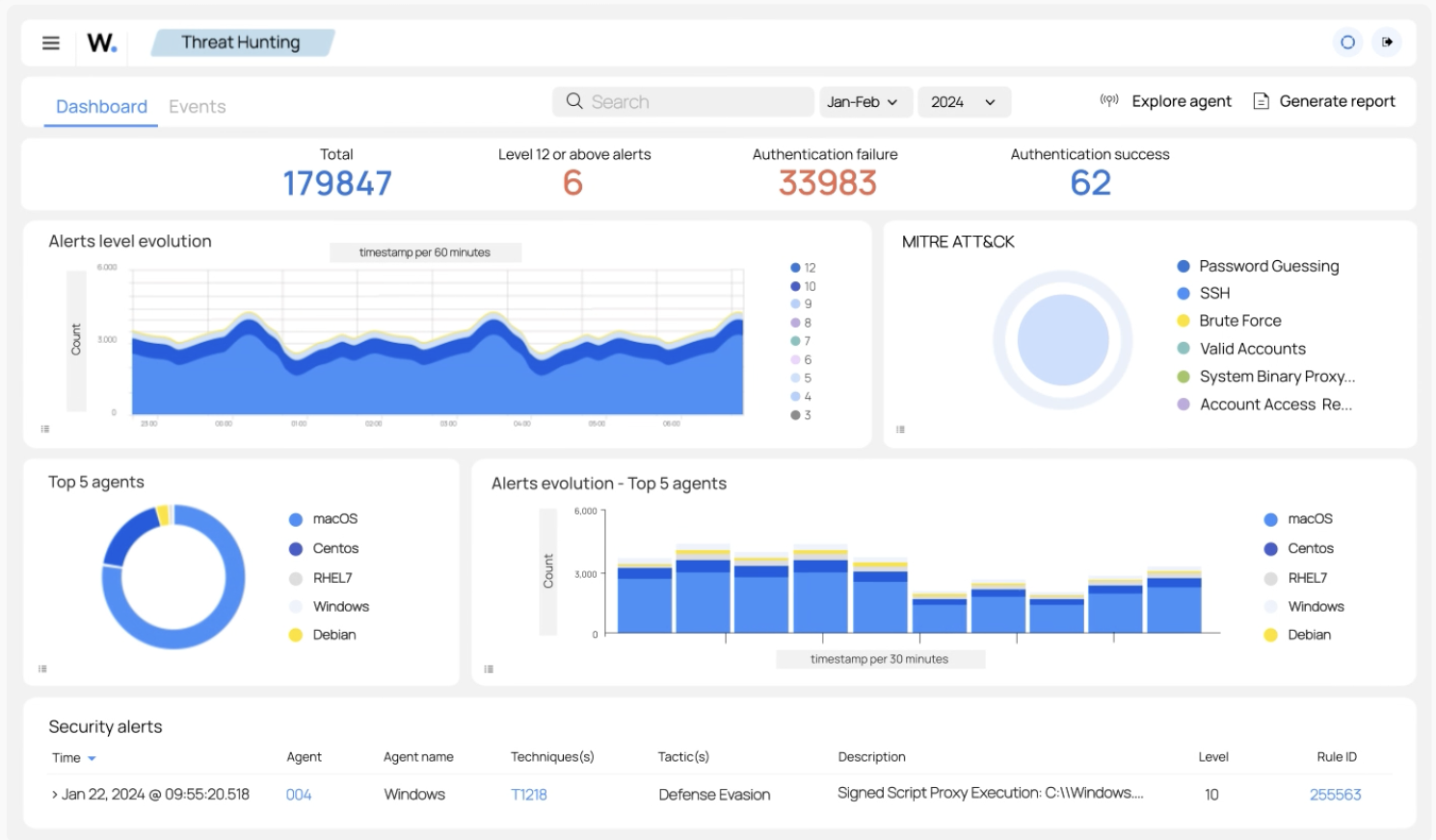
Continuous Endpoint Protection
A vulnerability assessment tells you where the holes are. Huntress makes sure nothing gets through them. We deploy Huntress managed EDR across your endpoints for 24/7 threat detection, incident response, and human-powered analysis by their Security Operations Center.
From ransomware attempts and persistent footholds to suspicious process chains, Huntress catches what traditional antivirus misses and gives our team actionable intelligence to respond fast.
- 24/7 managed detection and response (MDR)
- Human-analyzed threat intelligence from Huntress SOC
- Real-time agent health and incident tracking dashboard
- Catches ransomware, persistent footholds, and living-off-the-land attacks
Why Choose Us for
Security Consulting?
Security is not a product you buy; it's a posture you maintain. We approach every engagement with the mindset of an attacker and the discipline of an engineer.
Our team brings decades of hands-on experience across wired and wireless networks, cloud environments, and hybrid infrastructure. We pair that expertise with industry-leading SIEM and threat intelligence platforms to keep you protected around the clock.
-
Vendor-Agnostic Advice
We recommend the best solution for your environment, not the one that pays us the highest commission.
-
Actionable Reports
Our reports include clear remediation steps prioritized by risk, not just a list of CVEs and technical jargon.
-
Follow-Through
We don't just hand you a report and walk away. We help implement fixes and retest to confirm remediation.
Documentation-First Approach
Every security assessment, finding, and remediation step is documented and tracked. Automated integrations keep security posture documentation current as your environment changes.
From Our Insights
Security Assessment + Managed Services
Get a complimentary netvuln-tool security assessment when you sign up for managed services. See your real risk posture before we start managing your environment.
Ready to Strengthen Your Security Posture?
Don't wait for a breach to discover your vulnerabilities. Let our team assess your environment and build a roadmap to a more secure future.
Request Your Complimentary Security Assessment