
Cybersecurity
5 Common Security Mistakes SMBs Make
Discover the critical security gaps that could be putting your business at risk and how to fix them.
Read More →Practical guides, expert analysis, and actionable advice on cybersecurity, IT strategy, and business technology for growing organizations.

Cybersecurity
Discover the critical security gaps that could be putting your business at risk and how to fix them.
Read More →
Cloud Services
We break down the pros and cons of using multiple cloud providers for enhanced flexibility and resilience.
Read More →
IT Strategy
Learn how virtual CIO services can align your technology with your long-term business objectives.
Read More →
Cybersecurity
Understand how SPF, DKIM, and DMARC protect your business email from spoofing, phishing, and invoice fraud.
Read More →
Cybersecurity
Learn why password reuse is your biggest vulnerability and how Keeper protects your business with zero-knowledge security.
Read More →
Cybersecurity
Discover why human error causes the vast majority of breaches and how uSecure turns your team into a human firewall.
Read More →
Networking
Discover how Tailscale enables zero-trust networking across mobile, desktop, and server environments with WireGuard-based encryption.
Read More →
Case Study
How Bullium Consulting delivered four years of data center modernization, disaster recovery, and renewable energy deployments.
Read More →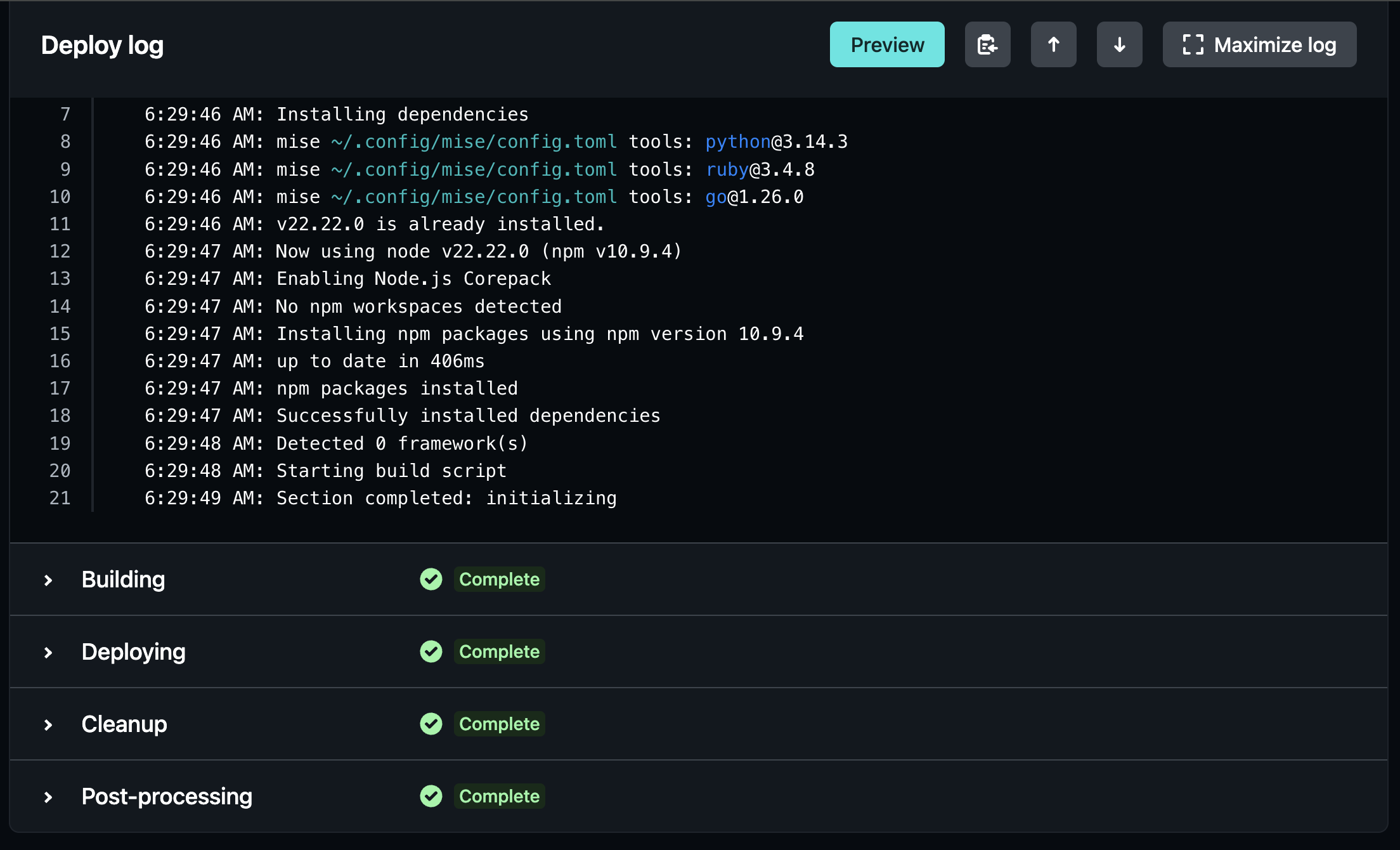
Web Development
A structured development process with dedicated teams, proven methodology, and full version control.
Read More →
Cybersecurity
A step-by-step guide to scanning your network for vulnerabilities, interpreting results, and building an ongoing security cadence.
Read More →
IT Strategy
Compare managed IT and break-fix support models to find the right fit for your budget, risk tolerance, and growth plans.
Read More →
Cybersecurity
Compare scanning approaches and discover how netvuln-tool bridges the gap between open-source transparency and commercial polish.
Read More →
Cybersecurity
Most businesses are surprised by the results. Here is what click rates, report rates, and credential submissions tell you about your real security posture.
Read More →
Cybersecurity
Learn how to map vulnerability scan findings to the compliance frameworks that matter for insurance, vendor questionnaires, and audits.
Read More →
IT Strategy
Seven evaluation criteria that separate a strategic technology partner from someone who just keeps the lights on.
Read More →
Cybersecurity
What topology mapping reveals about your network security that traditional diagrams miss.
Read More →
Infrastructure
Our 7-step methodology for validating every technology recommendation in a dedicated lab environment.
Read More →
Infrastructure
A practical comparison from an operator who has deployed both platforms at scale.
Read More →
Infrastructure
Distribution selection, security hardening, monitoring, and automation for business Linux environments.
Read More →
Infrastructure
Stop configuring servers by hand. A practical guide from practitioners who automate their own infrastructure.
Read More →
Infrastructure
Hardware recommendations, Proxmox configuration, and Ansible automation for a production-grade lab.
Read More →No articles found for this category.
Our team is here to help. Whether you need a security assessment, IT strategy guidance, or managed support, we're ready to talk.